Press Release
September 22, 2021
Digital Arts Inc.
Independent analysis of phishing domains in the first half of 2021 finds Amazon to be most frequently used word.
—Many of the top phishing domains can be obtained inexpensively or for free—
Information security solutions provider Digital Arts Inc. (headquarters: Chiyoda-ku, Tokyo, Japan; CEO: Toshio Dogu; hereinafter referred to as “Digital Arts”; Code 2326) is pleased to announce the release of a report on domestic and international phishing domains collected in the first half of 2021.
As use of internet shopping has increased with people staying home due to the pandemic, the number of phishing sites has been on the rise*1. In addition, some phishing sites are using the topic of COVID-19 to deceive people about vaccinations and stimulus payments.
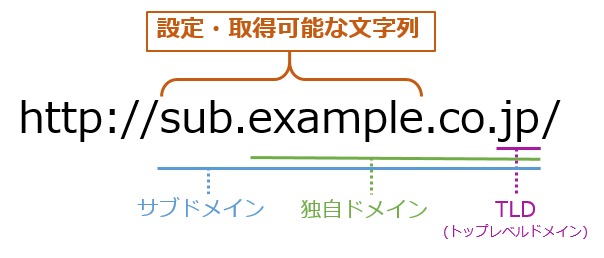
Digital Arts researches and collects information on various sites on a daily basis. For this report, Digital Arts compiled a list of domestic and international phishing domains discovered in the first half of 2021 (January to June) (*excluding IP address format URLs). The domains covered in this report are defined as in [Figure 1].
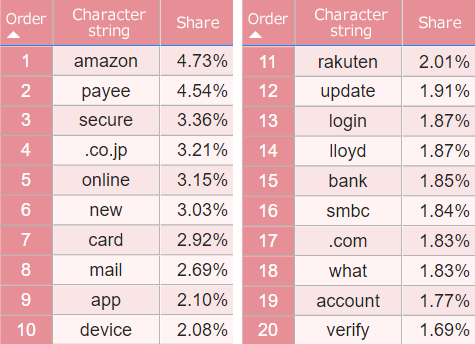
Amazon was the most frequently used word in phishing domains, with words related to online shopping, banking, and payment also topping the list.
In the "configurable/obtainable string portion" of both the original domain and the subdomain, the results were broken down into as many meaningful words and strings as possible and tabulated for each (for the case of using Dynamic DNS or Web hosting sites, only the configurable string portion of the subdomain is tabulated), resulting Amazon to be number one. In addition, many words related to online shopping sites, banking and payments, and words used in webmail services and secure logins also ranked. The ranking of ".co.jp" and ".com" is due to the fact that these were not used as TLDs (Top Level Domains) but as subdomains.
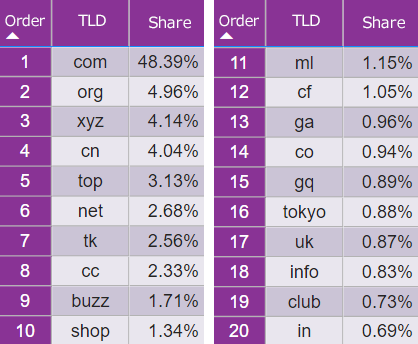
Many phishing sites use TLDs such as ".xyz" and ".tk," which are inexpensive or free to acquire.
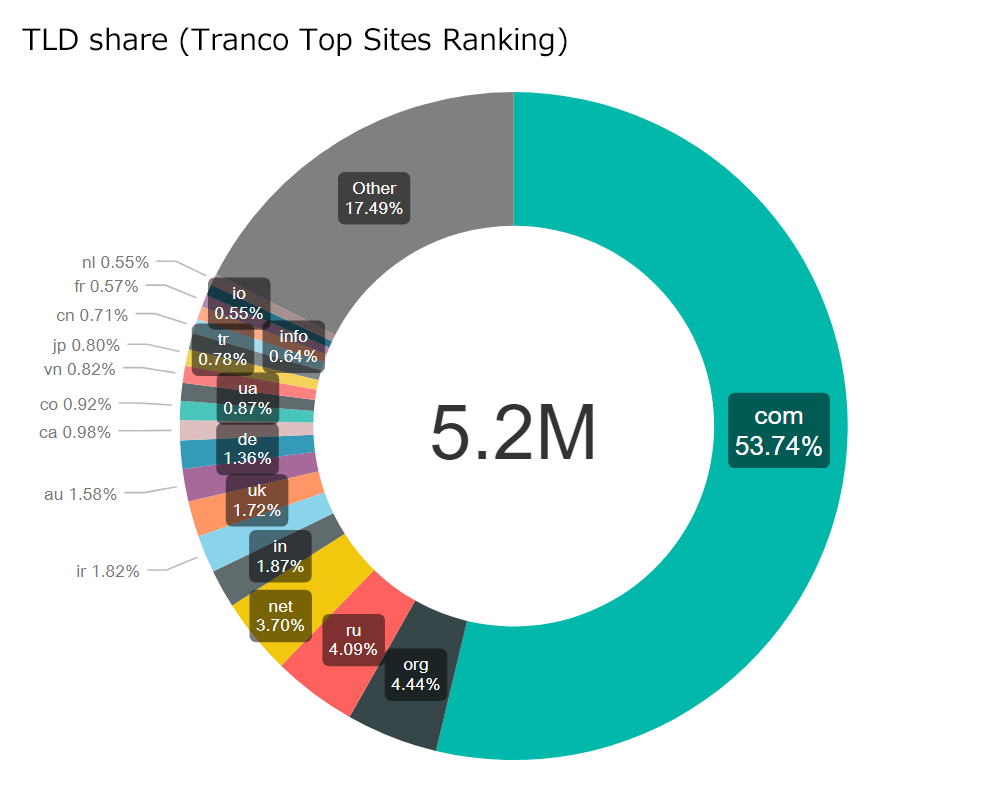
According to the IANA*2 Root Zone Database, there are 1,589 TLDs in the world as of August 2021. Based on Tranco's top site ranking of approximately five million domains, the TLDs as of August 9, 2021 were tabulated, and as shown in [Figure 3], ".com" ranked first with 53.74%, which is more than half of the global TLD market share. The second largest TLD share was ".org" at 4.44% followed by ".ru" at 4.09%. ".jp" had about 0.80% of the total TLD share.
In the the phishing domains collected by Digital Arts ([Figure 4]), first and second place were the same as the global TLD share. However, third place and lower were dominated by TLDs such as ".xyz" and ".tk," which are inexpensive or free to acquire.
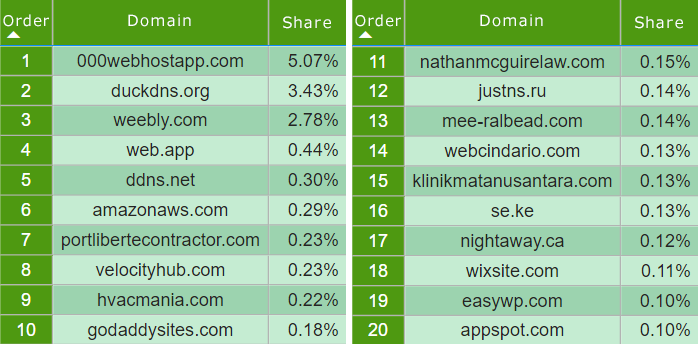
Domains offered by free web hosting services and dynamic DNS services top phishing site owned domains.
In [Figure 5], phishing site owned domains collected by Digital Arts, the domains of free web hosting services and dynamic DNS services are ranked at the top. These services are being exploited by attackers because anyone can create and use subdomains. Phishing sites often dispose of the domains they have acquired, but they also exploit the subdomains of free services.
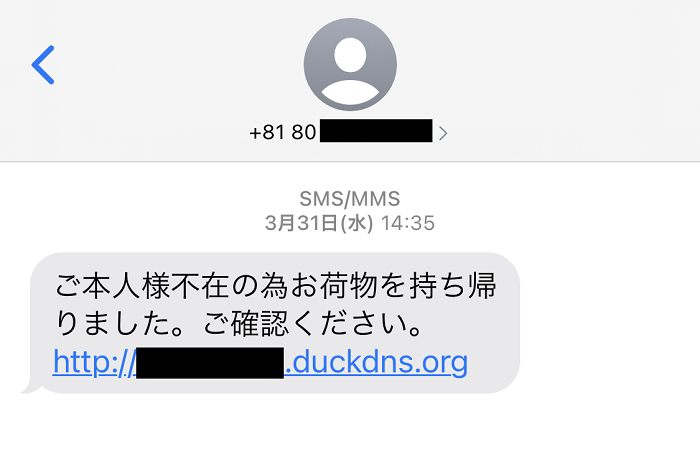
Among them, duckdns.org (3.43%), which ranked second, accounted for the majority of phishing sites using .org as the TLD. Fake textmessages, as shown in [Figure 6], which have claimed many victims across Japan, have been confirmed to be a common phishing tactic. While still ranking, lower-ranking domains have a small share of the market. This is probably because phishing sites as a whole acquire their own domains and then dispose of them, so they don't reuse the same domains multiple times, so they are dispersed in the aggregate.
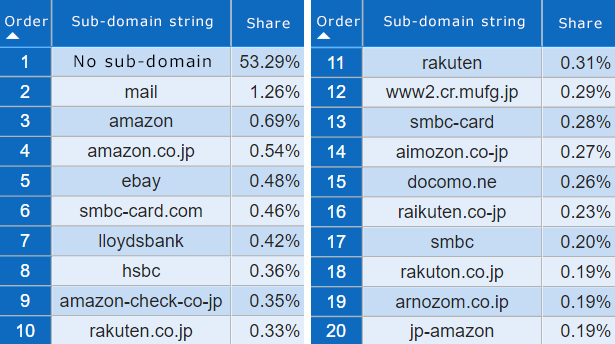
More than half of phishing sites do not use subdomains, while some use branded legitimate domains as subdomains.
When we counted only the subdomain strings (the part of the subdomain that excludes its own domain), we found that more than half didn't use subdomains. However, for those that used subdomains, we confirmed that many not only use brand names as a subdomain but also use the brand's regular domain as a subdomain, as shown in [Figure 7]. Some of these domains were only a few characters different from actual domains.
- *1 Accordingto a report by the Council of Anti-Phishing Japan, the number of phishing URLs in December 2019 was 2,178. However, by the time the pandemic hit in March 2020, the number was 4,136. Since then, the number of has been hovering between 4,000 and 6,000 per month, reaching 9,024 in August 2021.
https://www.antiphishing.jp/report/monthly/202108.html - *2 IANA was an organization that managed internet resources such as domain names, IP addresses and AS numbers, and protocol names and numbers used in different protocols. It was taken over by ICANN, a non-profit public interest corporation established to manage and coordinate internet infrastructure resources on a global scale. IANA is now used as the name of a function of ICANN. https://www.iana.org/domains/root/db
Digital Arts' i-FILTER blocks phishing URLs.
Digital Arts collects data on a daily basis from a variety of sources. In i-FILTER Ver. 10, phishing URLs are quickly sent to the filter database and swiftly blocked under the categories of "Phishing fraud" and "Illegal software and anti-social activities." Also, in light of the malicious usage of dynamic DNSs, the "Dynamic DNS" category has been set to "Block" in the basic settings of the category template. For URLs that arenot in the filterdatabase, Whitelisting can be used to block unknown phishing sites and malicious URLs by allowing access only to URLs that have been confirmed as safe by Digital Arts. In addition, the "Credential Protection" feature can block phishing sites that are set up on sites tampered sites that are difficult to distinguish from legitimate sites when users go to submit their login and password information.
The new standard for security measures: Whitelisting
i-FILTER Credential Protection https://www.daj.jp/bs/i-filter/#if_02_f02
Click here for the report on the aggregation of phishing domains for the first half of 2021.
The following is available on our site.
SecurityReport: "Phishing Domain Aggregation for the First Half of 2021
https://www.daj.jp/security_reports/210922_1/
Press Release: "Corona Flight Scams and Phishing Scams Are Rampant"
- Digital Arts Inc. Overview
- Digital Arts Inc. is an information security solution provider focused on the development and sales of security software for web, e-mail, files and other uses.
Since its founding in 1995, the company philosophy has been “Contributing to a safer, better, more convenient internet lifestyle" and since developing web-filtering software to prevent the browsing of harmful information on the internet, the company has been promoting internet security products to companies, the public sector and homes everywhere
Otemachi First Square, West Tower 14F, 1-5-1, Otemachi, Chiyoda-ku, Tokyo, Japan URL: https://www.daj.jp/