Press Release
January 26, 2021
Digital Arts Inc.
Emotet Detections up 4.5 Times in 2020
- New "i-FILTER®" and "m-FILTER®" features block threats from the forecasted "third wave" -
Information security solution provider Digital Arts Inc. (headquarters: Chiyoda-ku, Tokyo, Japan; CEO: Toshio Dogu; Securities Code 2326) is pleased to announce that we have released the analysis information on e-mails and URLs that are thought to have been infected by the malware Emotet. This comes after the number of e-mails and URLs detected by our web security software i-FILTER Ver. 10 and e-mail security software m-FILTER Ver. 5 to have been infected with Emotet increased by approximately 4.5 times in 2020.
Continuing to evolve since the first report of its existence in 2014, the malware Emotet steals information such as e-mail accounts and contact lists and has used it to attack numerous domestic companies and organization with ransomware and other viruses. Emotet's main method of infection is through executing macros from e-mail attachments or from files downloaded through URLs included in e-mails. However, since August 2020, cases of anti-virus software being evaded through the use of password protected ZIP files have also been confirmed.
Until now, our web security product i-FILTER Ver. 10 and email security product m-FILTER Ver. 5 have delt with the latest Emotet methods and used "whitelisting" to block access to URLs that are thought to be infected with malware, protecting all of our users and allowing us to achieve zero damage reports so far.
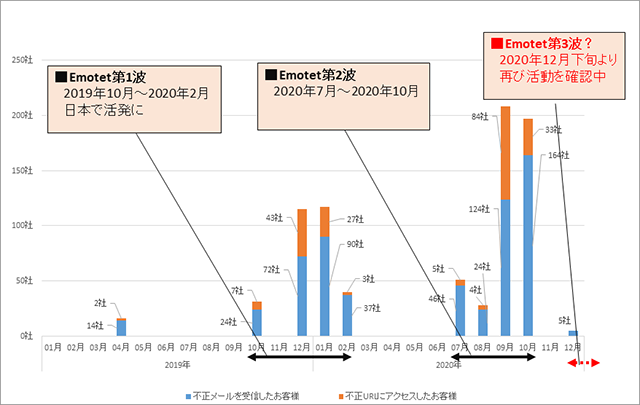
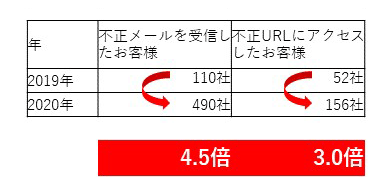
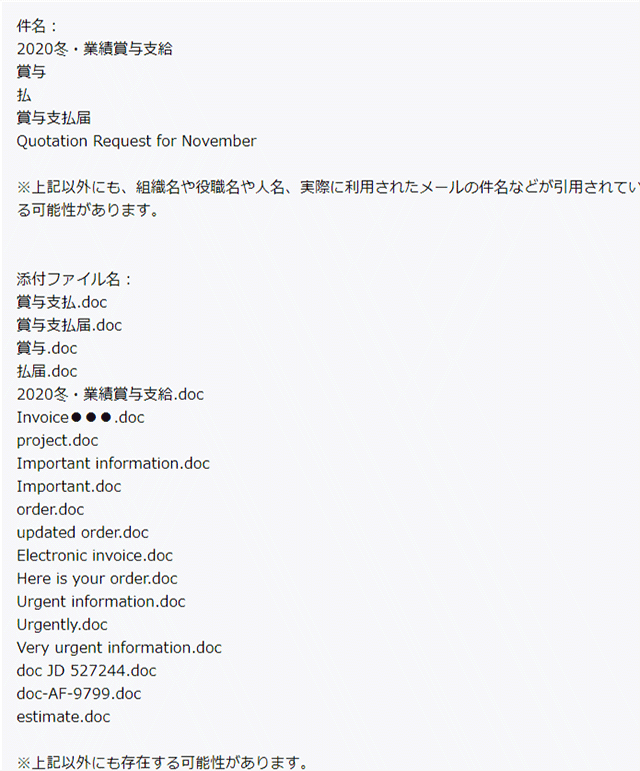
In addition, we have touched on the methods and number of infected cases of Emotet in the past. The number of customers who received emails that seemed to be infected by Emotet in 2020 was 490, which was approximately 4.5 times that of 2019. The number of customers who were seen to have accessed infected URLs was 156, which was approximately 3.0 times that of 2019 [Fig. 1]. The first wave of infections spans around four to five months from October 2019 to February 2020, the second from July 2020 to October 2020, and there is a high possibility that the confirmed cases in December 2020 will be the third wave. On our website, we have published the characteristics and features of the subjects, attachments, URLs, etc. of the emails used in attacks.
Emotet causes damage by using stolen information to pose as replies to real emails or work-related emails. However, in the first wave, it began using websites that were rigged as a stepping stone for its spread and in the second wave, used password-protected ZIP files. These are just some of the ways in which it continues to periodically change its methods of attack. In addition, Emotet targets are not limited by the size or industry of an organization, so we recommend taking this information, being cautious and using our products to take the appropriate measures.
Emotet's methods and Digital Arts products' transitional support
- September 2019:
- Confirmation that the majority of download URLs use legitimate websites that have been tampered with.
- July 2020:
- 1 device 1-year edition of "i-FILTER for Multi-Device" / 1 device 3-year edition of "i-FILTER for Multi-Device"
- Counterable with i-FILTER Ver.10's "whitelisting" and download filter function
Web Security Product i-FILTER details
E-Mail Security Product m-FILTER details
Information Analysis of the Malware Strain Emotet
The following is available on our corporate website.
Published page
Cyber risk information service "D Alert"
- Digital Arts Inc. Overview
- Digital Arts Inc. is an information security solution provider focused on the development and sales of security software for web, e-mail, files and other uses.
Since its founding in 1995, the company philosophy has been "Contributing to a safer, better, more convenient internet lifestyle" and since developing web-filtering software to prevent the browsing of harmful information on the internet, the company has been promoting internet security products to companies, the public sector and homes everywhere.
https://www.daj.jp/